The rapid convergence of Artificial Intelligence (AI) and decentralized cryptographic architecture has created one of the most critical technology paradigms of the decade: the intersection of Crypto Data Online and autonomous machine intelligence. As AI agents increasingly manage high-value financial networks, sensitive medical diagnoses, and critical national infrastructure, securing these models has become a paramount global priority.

The Core Vulnerabilities of Modern AI Systems
As AI applications scale across global industries, they introduce unique structural attack surfaces that legacy security frameworks cannot protect. These vulnerabilities fall into three primary categories:
- Data Poisoning Attacks: Machine learning models are entirely dependent on the quality of their training data. If an adversary introduces malicious or manipulated data into an online training pipeline, the AI will learn flawed behaviors, resulting in compromised outputs or hidden backdoors that can be exploited later.
- Model Theft and Reverse Engineering: Advanced AI models cost millions of dollars to train, representing immense intellectual property. Hackers target central model repositories or intercept active API queries to reconstruct and steal the underlying neural network structures.
- Inference Data Leakage: When a user inputs private information into a cloud-hosted AI tool (such as proprietary source code, legal briefs, or patient health summaries), that data is often processed in an unencrypted state on the host server. This exposes the raw information to cloud breaches and insider threats.
Crypto data online addresses these structural risks by wrapping the entire AI lifecycle—from data ingestion to model execution—in an unbreachable cryptographic layer.
Cryptographic Data Provenance: Preventing Data Poisoning
To ensure an AI model makes accurate and secure decisions, developers must verify the absolute authenticity of the training data. Crypto data online solves the data poisoning problem by anchoring data ingestion to decentralized blockchain ledgers.
When data is collected across the web or from connected edge sensors, it is instantly stamped with a unique cryptographic hardware signature. The metadata, lineage, and hash of the dataset are then recorded onto an immutable blockchain ledger.
Before the AI training engine processes any information, it references the ledger to confirm that the dataset has not been altered, deleted, or injected with malicious inputs. This creates a transparent, tamper-proof audit trail for data provenance, ensuring that the machine learning model is constructed on a verified foundation of digital truth.
Zero-Knowledge Cryptography: Verifying AI Model Integrity
In a world where AI algorithms dictate loan approvals, medical triages, and automated border security, verifying that an AI model actually executed a specific calculation without bias or unauthorized tampering is essential. This is achieved through the implementation of Zero-Knowledge Proofs (ZKPs).
Through ZK-ML (Zero-Knowledge Machine Learning), a cloud server can run a highly complex inference model on a user’s private dataset and generate a compact, mathematical proof (such as a zk-SNARK). This proof demonstrates with absolute mathematical certainty that:
- The specific, authorized version of the AI model was used.
- The model executed the calculation correctly based on the provided inputs.
- The underlying parameters of the model were not modified during runtime.
This verification occurs without the cloud host ever revealing its proprietary model weights to the client, and without the client needing to audit millions of lines of neural network code.
Fully Homomorphic Encryption: Secure AI Inference
One of the greatest historical barriers to using cloud-hosted AI for sensitive enterprise tasks was the necessity of decrypting data prior to processing. Fully Homomorphic Encryption (FHE) eliminates this vulnerability, enabling secure AI inference on fully encrypted data streams.
By leveraging FHE within a crypto-powered network, a financial institution or healthcare provider can encrypt sensitive data locally on an edge device and transmit it to a third-party cloud AI service. The AI model executes its analytical algorithms directly on the encrypted ciphertext.
The cloud server generates an encrypted output and sends it back to the client, who decrypts the final result locally using private keys. Throughout the entire transaction, the raw data is never exposed to the cloud provider, rendering server-side data breaches completely harmless.
Architectural AI Security Comparison Matrix
| Security Vector | Standard Cloud AI Infrastructure | Crypto-Powered AI Security |
| Data Provenance | Unverified web scraping; highly vulnerable to data poisoning. | Immutable data hashing and signature logging on blockchain ledgers. |
| Inference Privacy | Data must be decrypted on host servers during active processing. | Fully Homomorphic Encryption allows computation on ciphertext. |
| Model Verification | Black-box operations; no method to prove which model version ran. | Zero-Knowledge Machine Learning (ZK-ML) generates mathematical execution proofs. |
| Identity Access | Centralized API keys and passwords prone to credential theft. | Decentralized Identifiers (DIDs) verified via cryptographic key pairs. |
| Network Resilience | Centralized API servers; vulnerable to DDoS and target infrastructure breaches. | Decentralized hosting nodes with multi-party computation capabilities. |
Secure Identity and Access for Autonomous AI Agents
By 2026, the internet is heavily populated by Agentic AI—autonomous software entities capable of making independent financial decisions, negotiating contracts, and communicating with other digital platforms. Securing the identities of these agents is paramount to preventing automated fraud and chaotic system escalations.
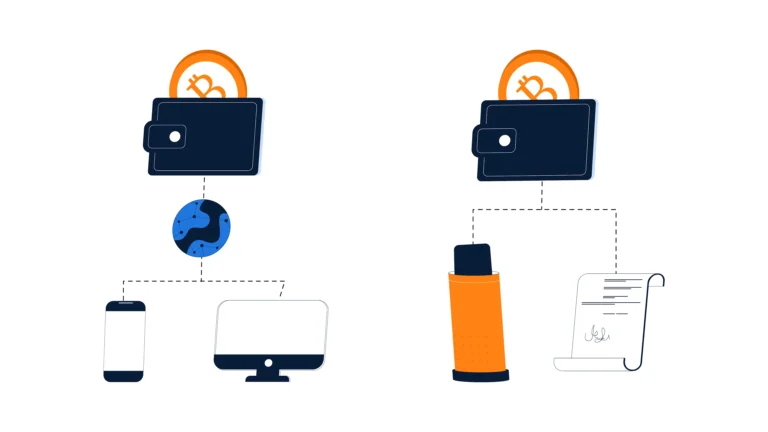
Advanced cyber networks address this by provisioning autonomous AI agents with their own unique Crypto Data Online Decentralized Identifiers (DIDs) and cryptographic wallets.
When an AI agent requests access to an enterprise database or initiates an international cross-border payment, it does not rely on human passwords. Instead, it signs the digital transaction using its own private cryptographic key pair. The underlying infrastructure verifies the signature against a decentralized ledger in milliseconds, confirming the agent’s identity, operational parameters, and explicit spending limits before granting network access.

Strategic Deployment Across Critical Sectors
The combination of crypto data online and smart AI safety protocols has transformed the security infrastructure of highly regulated global fields.
Defense and National Security
Military operations rely on distributed AI models deployed across drones, naval vessels, and tactical gear to parse real-time situational telemetry. By wrapping these edge AI models in post-quantum cryptographic tunnels, national defense structures ensure that adversarial foreign powers cannot spoof data inputs, jam communication networks, or reverse-engineer captured autonomous hardware.
High-Volume Financial Markets
In global banking and quantitative trading, AI algorithms execute millions of market transactions per second. Crypto-powered security systems log transaction results onto a distributed blockchain ledger, creating an alterproof financial audit track. Concurrently, defensive AI agents scan encrypted transactional data streams via homomorphic encryption, instantly neutralizing automated exploit attempts and flash-loan manipulation.
Precision Medicine and Healthcare
Pharmaceutical corporations use machine learning models to accelerate clinical drug discovery by analyzing immense volumes of genetic data. By applying secure multi-party computation (SMPC) alongside crypto data online, competing healthcare networks can securely combine their patient databases. This allows the AI models to train on a vastly larger dataset to find medical breakthroughs without exposing raw, private patient identities or violating strict international privacy mandates.
Real-World Engineering and Implementation Hurdles Crypto Data Online
While the strategic path forward is clear, scaling a crypto-powered AI defense infrastructure presents real-world technical and economic friction:
- The Computational Overhead Penalty: Running fully homomorphic encryption pipelines and compiling zero-knowledge machine learning proofs demands an immense amount of raw processing power. Organizations must deploy specialized cryptographic hardware acceleration, such as dedicated ASICs or custom GPU acceleration clusters, to keep network latency minimal. Crypto Data Online
- Developer Complexity and Tooling: Designing zero-knowledge circuits for complex deep learning models requires highly specialized mathematical and cryptographic expertise. However, the open-source community is rapidly bridging this gap by engineering modular software development kits (SDKs) and specialized compilers that convert standard Python AI models directly into cryptographically verifiable formats.
- Dynamic Regulatory Compliance: Legislative frameworks like the EU AI Act dictate that automated AI models must remain completely transparent and explainable. Security teams must carefully design their cryptographic layers to ensure that while data remains private and secure, automated system tracking logs remain accessible and auditable to satisfy compliance officers.
The Long-Term Horizon: Autonomous Self-Securing Crypto Data Online
The ultimate trajectory of crypto data online and artificial intelligence points toward completely autonomous, self-defending data ecosystems. Within these upcoming architectures, human system administrators will no longer manage daily network settings or manually patch software flaws.
Instead, defensive AI agents will continuously monitor global threat feeds, scan the dark web for emerging algorithmic exploits, and autonomously design, test, and deploy post-quantum cryptographic updates across their own decentralized infrastructure. This continuous optimization and defensive iteration will occur within seconds, permanently closing the human delay windows that cybercriminals rely on to execute data breaches.
Conclusion
Crypto Data Online has fundamentally redefined the future of AI security, shifting digital protection from an outer perimeter firewall into an active, self-protecting mathematical architecture. By anchoring data provenance to immutable blockchain networks, safeguarding inference pipelines with fully homomorphic encryption, and verifying model operations through zero-knowledge proofs, modern networks ensure that AI can scale safely without compromising corporate secrets or user privacy.
As automated, machine-driven threats continue to accelerate in both execution speed and complexity, relying on traditional human-led defense strategies is no longer viable. The security of global infrastructure depends on adopting these intelligent, mathematically verified, and decentralized frameworks—safeguarding the integrity of artificial intelligence and preserving trust within the global digital economy.